Key Takeaways
- Some skills to mention on your portfolio include:
- Technical skills such as cryptography and programming languages
- Tools and software proficiency such as Excel and Qualys
- Leadership and decision-making for managerial positions
- Risk assessment and management
- A risk register is a detailed document that you maintain regarding the risks associated with an organization’s network
- Having a risk register on your portfolio shows your critical and analytical capabilities to employers
- You can find risk register templates from:
- Smartsheet Free Risk Register Templates
- SecureFrame Template
- Project Manager Risk Tracking Template for Excel
- Tips for adding control tests to your cybersecurity portfolio:
- Document everything, including the test plan and methodologies
- Make sure present the findings of your test
- Give remedies and solutions to showcase problem-solving skills
- Mention the tools and scanners you use to show proficiency
- Best platforms for creating portfolios:
- GitHub
- Notion
- Wix
- Google Drive
Even as a fresh graduate with a bachelor’s degree in cybersecurity and risk management, you can land a good-paying job with the right portfolio. All employers in this industry are seeking candidates who have good knowledge of the practices and principles. Therefore, a portfolio speaks volumes for your expertise as well as eligibility for a good job.
However, as a beginner, it might not be very clear to you what is included in a cybersecurity and risk portfolio. So, in this guide, we go over the two most important components — risk register and control test artifacts — with a quick overview of other important parts of a portfolio. Let’s dig in!
Overview of Cybersecurity Portfolios for Graduates
| What to add in a cybersecurity portfolio? |
|
| What is a risk register? | A complete document that is used to record and monitor risks associated with an organization’s network |
| What is a control test? | One or more procedures are used to assess and evaluate whether the security protocols in an organization’s network are properly designed and functioning |
Why Do Cybersecurity Graduates Need a Portfolio?
Before you begin creating a portfolio from scratch, it is important to understand its function and purpose. While artistic or creative fields such as liberal arts graduates, have very obvious reasons for making a portfolio, it is not so obvious for a cybersecurity graduate.
Firstly, a portfolio for a cybersecurity and risk professional helps showcase very specific skills that are tailored to a particular job opening. For example, anyone looking for entry-level risk and security jobs as an Analyst will prefer to add relevant skills and competencies. Therefore, a portfolio makes sure you appear relevant and fit for a particular job.
Secondly, while portfolios can showcase skills and knowledge in theory, they are also excellent for showcasing hands-on skills. According to reports, 80% of hiring managers will hire someone based on their skills alone. So, this makes it clear that showing hands-on skills is vital, and portfolios play an important role here as well.
Thirdly, portfolios are typically a documented form of all the work you have done. As a result, it works as proof of everything you claim to know and have done, making your profile much more credible to the recruiters.
In addition to all of this, it is important to note that cybersecurity is one of the growing fields. According to Data USA, the growth rate of total degrees being awarded in cybersecurity is over 15%. Therefore, the competition for the job is fierce nonetheless. In this case, a portfolio is the saving grace, as it can help your profile stand out and outshine others easily!
In short, a portfolio is an excellent tool to not only present your skills, knowledge, and experience, but also work as a compelling tool that tells your professional and academic journey.
What Can I Add to my Cyber Risk and Cybersecurity Portfolio?
Of course, your basic details such as name, residency, age, and qualifications are a must-have for any type of portfolio. Whether you are using a digital portfolio or a printed one, this information has to be there. However, this is not enough to tell your professional journey to the recruiter. Therefore, you need to add much more substance.
From personal projects to cybersecurity and risk certifications to work experience, document everything to share with potential employers. So, here is a simple list of contents to add to your cybersecurity portfolio:
Core skills:
|
Personal projects:
|
Tools and software you can use:
|
Certifications (best for beginners):
|
In addition to this, the other two most important components of a portfolio that many cyber security and risk management graduates forget to add are risk registers and control tests. So, here is how you can add them to enhance your portfolio.
Risk Register for Cybersecurity Portfolio
A risk register is one of the most detailed and crucial documents you will be in possession of during your cybersecurity career. Firstly, understand that this is typically a “log” that you use to record potential, existing, past, and future cyber threats to an organization’s network system. So, all the risks you identify are documented in this catalog for reference, risk management, compliance, and security planning. Moreover, it highlights core features such as the likelihood of any risk, its impact, risk level, cause, and appropriate response.
Why is a Risk Register Important for Your Portfolio?
A risk register is a crucial part of your portfolio, especially if you are seeking jobs in GRC and SOC. Here are some benefits of using a risk register in your portfolio:
| Shows your understanding of real-world problems | Whether you have a mock-up risk register or one from a real business experience, it will showcase how in-depth your understanding of risk is, as well as other skills such as risk assessment and evaluation |
| Works as evidence | Most employers need to see proof for your GRC skills. Therefore, having a portfolio with risk registers makes you a strong candidate for most jobs |
| It demonstrates other skills | While the risk register itself is a technical task, it can showcase non-technical skills such as analytical capabilities, adaptability, problem-solving, and documentation |
| Risk frameworks | Most risk registers are built on the risk frameworks such as NIST and ISO. So, it goes on to show that have a thorough understanding of these essential frameworks |
Risk Register Sample and Guidelines
Following is a sample structure for an efficient and beginner-friendly risk register:
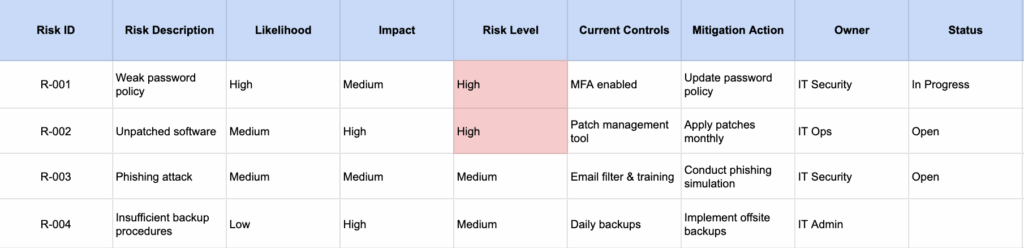
You can find an excellent variety of risk register templates online on various platforms, including:
- Smartsheet Free Risk Register Templates
- SecureFrame Template
- Project Manager Risk Tracking Template for Excel
Adding Control Test to Cybersecurity and Risk Management Portfolio

A control test in the world of cybersecurity is a crucial tool to document and assess the security measures that any organization puts in place for its cyber network. Moreover, most of the cyber control tests follow industry-wide risk frameworks, as well as focus on ensuring the security and governance within the organization.
In addition to this, both risk register and control tests are crucial parts of a cybersecurity professional’s day-to-day job. However, both are different in essence, as one is focused on identifying and documenting risks, while the other is focused on implementing the right security measures by testing them.
Since control tests are focused on testing and evaluating the network design and infrastructure, they require many skills such as analytical capabilities, critical thinking, planning, and understanding of risk frameworks. Therefore, having this in your portfolio is crucial. There are some types of common control test approaches in cybersecurity, including:
- Inquiry
- Performance
- Observation
- Inspection
- Computer-assisted audit techniques (CAAT)
Some common tests include:
- Penetration testing
- Application Security Testing (AST)
- Ethical hacking
What is the Importance of having Cyber Control Tests on Your Portfolio?
Including control test artifacts in your portfolio is highly valuable, especially if you are seeking job roles such as cybersecurity analyst, information security administrator, and cybersecurity risk manager. Here is why:
| Tangible evidence | Having control test artifacts in the portfolio basically acts as tangible or visible proof that you have worked on the application of important risk and security principles |
| Showcase analytical skills | A huge part of control tests involves analyzing the results and understanding what the test tells about an organization’s security measures. |
| Showcase technical knowledge | Many control tests are based on technical frameworks and principles such as NIST and ISO. Having it in your portfolio shows that you not only understand the technicalities in theory, but also in practicality. |
| Demonstrates professional documentation skills | Jobs like GRC/SOC Analysts require a lot of documentation, reporting, and data organization. Including control tests expertise in the portfolio can show your professionalism and ability to organize data efficiently. |
How to Add Cyber Control Tests to Cybersecurity Portfolio?
To add your experience with cyber control tests in your portfolio, focus on using documented exercises and work experience. If you are already working in the field as a professional, then use your existing work on control tests and add it to the portfolio as PDFs or images. However, if you are a beginner and do not have professional work, you can set up virtual labs at home, create mock companies, and use simulations to run control tests and document them. Here are some useful tips:
Document your work
Firstly, it is important to document everything you do. This includes even the test plan, tools, and software you use. Compile everything in a user-friendly document to present.
Plan your test
Make sure to create a plan for your control test. The plan sets the direction and context of your test, allowing potential employers to fully understand your goals and expertise. In the text plan document, mention the objectives, the controls, the methodology, techniques, and tools.
Collect your findings
A huge part of the test is the result. The results tell you so much about your controls and help you plan the next steps. So, you should focus on collecting the results in the form of graphs, screenshots, pie charts, and tables for easy readability. Don’t forget to make these part of your documentation as well.
Analysis
Finally, the analysis part is where you unleash your true potential. In this part, you give your own analysis and insights of the security controls, including problem identification, causes, proposed solutions, and next steps. Suggesting recommendations and remedies further showcases your ability to implement cybersecurity in real-life situations.
Platforms to use
You can use virtual labs offered in online cybersecurity programs, or set up your own. Here are some popular platforms for virtual labs and simulations:
Platforms for Cybersecurity Portfolios
Wondering where to start? Find the top platforms for creating technical cybersecurity and risk portfolios below:
| GitHub |
|
| Notion |
|
| Wix |
|
| Google Drive |
|
Conclusion — Make an Impressive Cybersecurity Portfolio
In conclusion, having a strong portfolio with ample information for employers is one of the most effective ways of finding cybersecurity jobs. Using the right tools and strategies can help you design an effective portfolio that will be usable across various job applications.
Moreover, you should focus on adding your strongest suits in the portfolio, be it theoretical knowledge or hands-on experience. For most cybersecurity degree jobs, reports indicate that the bare minimum required is a bachelor’s degree. Therefore, you should be able to kickstart your career by exploring the best colleges for a cybersecurity and risk degree by state. Assess factors like cost and program duration to make an informed choice and get started with your cybersecurity career!
Frequently Asked Questions (FAQs)
Are cybersecurity graduates in demand?
According to several sources, including Data USA, there has been an increase in reported data breaches in recent years. This tells us that there is a growing need for more qualified cybersecurity individuals who can tackle this growing threat. In addition to this, BLS reports that there is 24% job market growth expected for this field. Therefore, it is very easy to say that the cybersecurity graduates are in high demand and will continue to be so.
How to learn cybersecurity control tests?
Learning to run cybersecurity control tests begins with developing structured fundamentals and ensuring strong basic concepts. Therefore, it is a highly specialized skill that comes after years of education and work/practice. For this reason, we recommend enrolling in a professional degree, such as a cybersecurity bachelor’s program from a renowned college. Within these programs, you will be mentored by qualified lecturers and teachers who are guaranteed to teach you the core concepts over a span of 3 to 4 years. In addition to this, you can also explore certifications to further accelerate your learning journey.
Get College Recommendations Here
What is the difference between a cybersecurity portfolio and a resume?
Here are the main differences between a cybersecurity resume and a portfolio:
| Resume | Portfolio |
| Provides a quick overview of your qualifications, skills, and expertise | Provides an in-depth look into each and every skills and expertise you have mentioned |
| Typically very concise and a maximum of 2 pages | Can include more than 2 pages and is not only text-based |
| Might not include supporting documents such as PDFs and images | Includes several supporting documents that help further demonstrate your capabilities |
| Has a formal and fixed structure/format | The format and structure is flexible and depend on the person |
What is the difference between risk assessment and risk register?
The main difference between risk assessment and register is that risk assessment is an activity to identify, evaluate, and manage risks, while a risk register is a document that records all identified risks. While these two may be necessary to work side-by-side, they both offer different functions and fulfil different purposes. So, risk assessment is a process and a risk register only tracks and documents the findings of risk analysts.
